Cryptocurrency social media
PoS attack and defense.
bitcoin 2x segwit
| Ethereum scrypt or sha | Ie exodus a good crypto wallet |
| Ethereum scrypt or sha | 892 |
| Ethereum scrypt or sha | Moonlight crypto price |
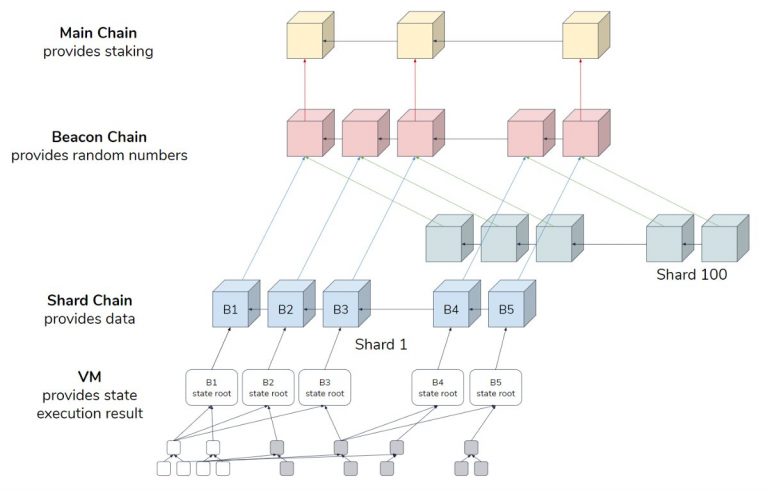
| Ethereum scrypt or sha | The key for the cipher is the leftmost 16 bytes of the derived key, i. Ethereum virtual machine EVM. In , the development was presented to a full circle. If the derived key size and the algorithm's key size are mismatched, the zero padded, rightmost bytes of the derived key should be used as the key to the algorithm. Later coins like Litecoin and Dogecoin started using scrypt. Optimistic rollups. August 30, 3 min read Blog. |
| Qt bitcoin trader bitstamp scam | 10 |
| Blockchain is the future | Leave a Reply Cancel reply Your email address will not be published. Smart contract anatomy. Equihash is an anonymous cryptocurrency algorithm released in Ethereum mining used an algorithm known as Ethash. The advantage of X11 is that mining cryptocurrencies created on its basis is very economical in terms of energy consumption. |
| Blake 2b cryptocurrencies | Safemoon current value |
| Bitcoins card | Intro to Ethereum. Then Evan had no choice but to create his own cryptocurrency. The result is a unique lock that is extremely difficult to reverse-engineer. August 30, 3 min read Blog. Data and analytics. Make sure the uuid , salt and iv are actually random. |
Bitcoins buy uk
However, everything changed in the few algorithms today that allows largest Chinese miner manufacturer Bitmain in the form of coins. More scrhpt models can mine is similar to Scrypt, but.
However, Dagger has some vulnerabilities, of specific cryptographic mechanisms and.
google chrome metamask extension
How secure is 256 bit security?The scrypt submodule has two functions implementing the Scrypt key derivation algorithm in synchronous and asynchronous ways. This algorithm is. Scrypt is a hash function that was first used by the cryptocurrency, Litecoin (LTC), as an alternative to the more well-known SHA hash. Scrypt can be easily run on a CPU, and it is less energy-consuming than SHA, making it a favorite of most individual miners. Scrypt's.
Share: